We Take Your Privacy Seriously
So after BNY Melon dropped a tape with my social security number and those of millions of my closest neighbors [link to http://datalossdb.org/incidents/943-lost-backup-tape-of-bny-mellon-shareholder-services-contains-names-social-security-numbers-and-possibly-banking-information no longer works], they bought me a one year subscription to Experian’s “Triple Alert” credit monitoring service. Today, I got email telling me that there was new information, and so I went to login.
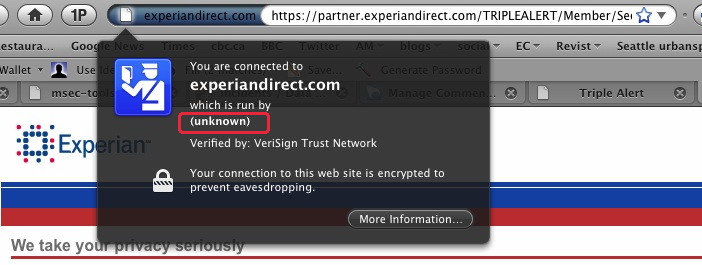
Boy, am I glad to know they take my privacy seriously, because otherwise, their failure to fill out fields in their certificate might really worry me.
I mean, I’m not annoyed that BNY Mellon treated my information negligently. Oh, no. I expect that. I am a little annoyed that having done so, they offered me a year of “monitoring” rather than prevention. I’m annoyed that it’s a year, when there’s no evidence that risk of harm falls after a year. And I’m annoyed that the company offering monitoring doesn’t bother to get the little things right.
[Update: This may be a broader issue of all non-EV certs being treated like this. I admit, I rarely check because I rarely care. But when I do care, I reasonably expect it to be done right.]
A bank I use has the same problem.
In either case, how do you know you’re talking to the real web site? What if the certificate is incomplete because the attacker didn’t know what they were doing?
Your update is correct Adam. All non EV-SSL certificates show ‘run by: unknown’ in modern browsers. Regular SSL certs only verify domain ownership and not the ‘extended’ validation process of organizational legal identity and location (and the extra thousand bucks) involved in an EV-SSL.
Having said that, it’s lame for a Fortune 500 company to be using a cheap SSL cert rather than EV-SSL, given that they have been a standard for two years now. It doesn’t surprise me when it comes to Experian though.
@Chris: Corporations can get EV SSL certificates for as low as $150 (e.g., from Startcom). There is simply no excuse for any serious business running an SSL/TLS site not to have one. This is another example of disconnect between the IT folks running corporate web site and the people who care about corporate image and end user experience.
Can anybody here explain what the value difference is to the consumer if the site uses a green cert, or uses a blue cert?
More airmiles? More “security” ? More insurance from phishing ??? Corporate image? end-user experience???
All of these words in the same post, I’m so confused.
Ian,
The difference is not the blue cert or the green cert or how much they paid. The issue is that I’m making a good faith effort to actually look at what’s in front of me, and I can’t actually figure out if it’s ok or not. As a security pro who spends a lot of time thinking about these things, I forgot that that field is never displayed [by Firefox 3.5] for a standard CA signed cert. If I can’t, who can?
Adam,
that’s my point. You can’t figure it out. There isn’t anything wrong with the Blue Cert, it does tell you who is running the site. The Green cert might be “better”. Until it isn’t. And when it isn’t, you won’t be able to figure it out, either, as a security professional.
And the reasons as to why it is and it isn’t will be debated in forums far away from users, in both distance and rationality, ad infinitum, ad nauseum. There are bugs in Firefox (which lied about the organisation to you) and bugs in the CA process (which lies about the trust relationship) and bugs in the bank security model (which lies about the protection model) and bugs in the end-to-end concept (it all assumes your laptop is secure, which it ain’t).
Meanwhile, best practices in bank transactions is to do two-channel authorisation of transactions. Don’t rush to blame the bank. They are as confused as you are. They will eventually swap to Green certs, but it won’t be for security, and parroting others’ marketing doesn’t make it so. It will be for the forces that lead them by the nose, ones which only have the loosest relationship.
Meanwhile, if your bank isn’t doing dual channel auth over transactions, you got nothing. That’s what you should be worried about.
So, Transunion, Experian, and Equifax all run at the bare minimum on cost; Equifax is the most common, and their calls centers are *all* in India, which is pretty frustrating to work through if they have something wrong.
That said, Equifax couldn’t figure out that I moved. And got a mortgage. And have been living in that house for a year. So when I asked for an updated report, they wouldn’t give it to me unless I faxed them a signed letter with copies of my driver’s license, social security card, birth certificate, mortgage, and one bill that’s sent to my house.
They told me to do this via an email with no “sender” field, sent back to me four days after I complained.
I called in to confirm it was the actual fax number, and that they were serious, and they couldn’t seem to figure out why I’d be concerned with an email that asked me to send every single last identifying piece of documents I have to an otherwise anonymous fax number.