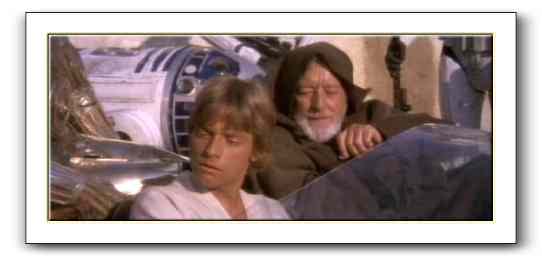
"You Don’t Need to See His Identification"
Well, here we are, on a list of top influencers in information security [link to http://www.itsecurity.com/features/top-59-influencers-itsecurity-031407/ no longer works], and we’ve barely said welcome to any new readers! Welcome!
If you’re just showing up, we’d like to influence you to understand that identification rarely solves security problems by itself.
I posted “You Don’t Need to See His Identification,” using a famous scene from Star Wars to illustrate a point, and followed that up with a series using scenes from “Star Wars to Illustrate Security Principles of Saltzer and Schroeder.” You might enjoy it. We try to inject humor into the blog, you might enjoy our Amusements category archive. If you’d like some deeper thinking, the breach analysis category has, I think, been good recently, or you can feel free to explore.
Incidentally, Tom Ptacek influenced me to think about the nature of the list, with his post “Take me off your list” [link to http://www.matasano.com/log/723/take-me-off-your-list/ no longer works], and he does so using the term ‘flattery attack.’ That sounds, to me, like a variant of Schneier’s ‘publicity attack,’ and that reminds me of my co-blogger Mordaxus asking “Let’s Stop Cutesy Names for Attacks.” Perhaps we’re not so influential as we hope.